
All figures (13)
 Table 9. Subprotocol πS,AV
Table 9. Subprotocol πS,AV Table 12. Subprotocol πans
Table 12. Subprotocol πans Table 7. Subprotocol πencr
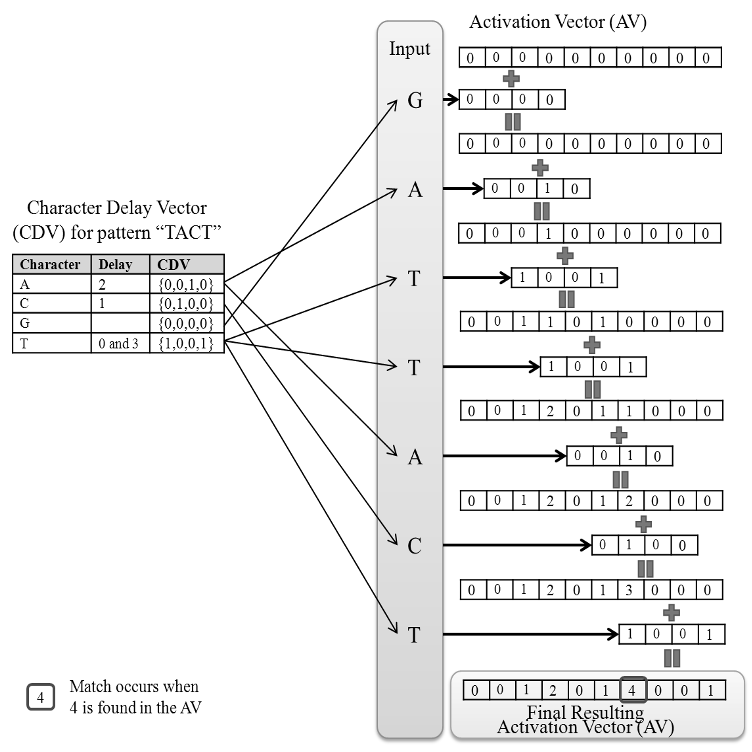
Table 7. Subprotocol πencr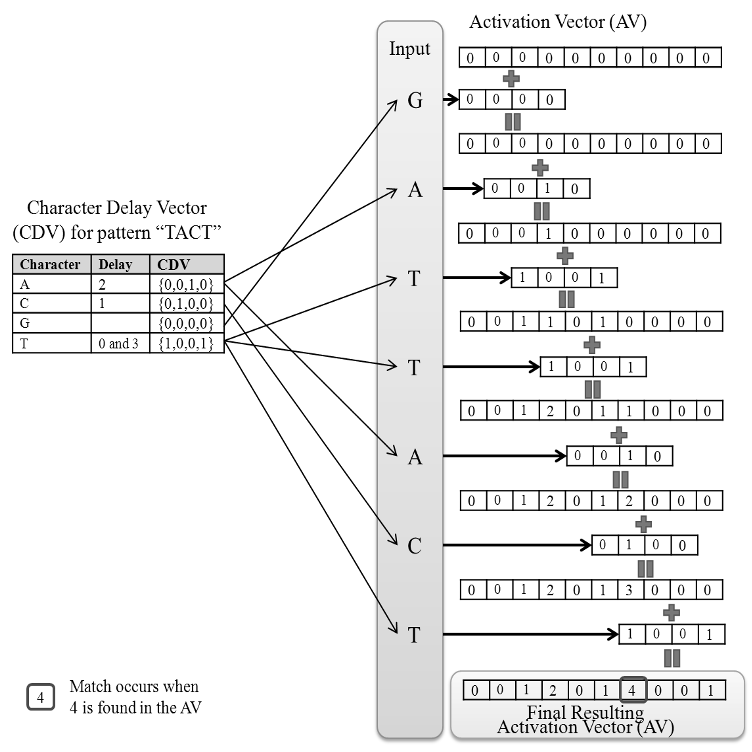 Fig. 1. Example of IPM’s operation
Fig. 1. Example of IPM’s operation Table 5. Overview of 5PM protocol for HBC adversary model, πH5PM . See Table 4 for notation.
Table 5. Overview of 5PM protocol for HBC adversary model, πH5PM . See Table 4 for notation. Table 8. Subprotocol πC,AV
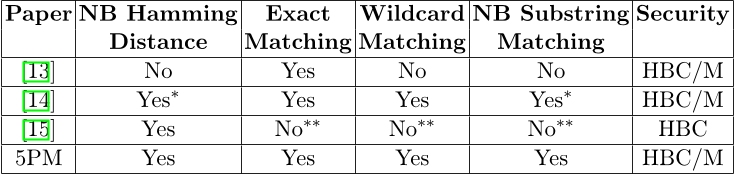
Table 8. Subprotocol πC,AV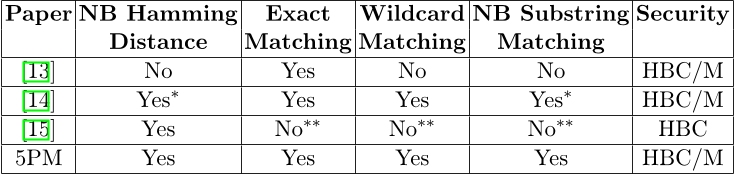 Table 1. Comparison of previous protocol functionality, NB=non-binary HBC=honest but curious, M=malicious, *=using unary encoding and additional tools, **=can be extended
Table 1. Comparison of previous protocol functionality, NB=non-binary HBC=honest but curious, M=malicious, *=using unary encoding and additional tools, **=can be extended Table 4. Notation used for 5PM protocols
Table 4. Notation used for 5PM protocols![Table 2. Detailed comparison with [14] and [16] for single-character wildcards and substring matching in malicious model with text length=n, pattern length=m, security parameter=k, rounds=Rds.](/figures/table-2-detailed-comparison-with-14-and-16-for-single-xf61t5xw.png) Table 2. Detailed comparison with [14] and [16] for single-character wildcards and substring matching in malicious model with text length=n, pattern length=m, security parameter=k, rounds=Rds.
Table 2. Detailed comparison with [14] and [16] for single-character wildcards and substring matching in malicious model with text length=n, pattern length=m, security parameter=k, rounds=Rds.![Table 3. Detailed comparison with [15] for non-binary substring matching in HBC model with text length=n, pattern length=m, security parameter=k, rounds=Rds.](/figures/table-3-detailed-comparison-with-15-for-non-binary-substring-2o93ac7o.png) Table 3. Detailed comparison with [15] for non-binary substring matching in HBC model with text length=n, pattern length=m, security parameter=k, rounds=Rds.
Table 3. Detailed comparison with [15] for non-binary substring matching in HBC model with text length=n, pattern length=m, security parameter=k, rounds=Rds. Table 6. Notation used in subprotocols in Tables 7 through 12
Table 6. Notation used in subprotocols in Tables 7 through 12 Table 11. Subprotocol πrand
Table 11. Subprotocol πrand![Table 13. Performance results for 1024 and 2048 bit key length in seconds for different settings of the alphabet Σ, the pattern p and the text T using fast-decryption Paillier [40].](/figures/table-13-performance-results-for-1024-and-2048-bit-key-juynvcjx.png) Table 13. Performance results for 1024 and 2048 bit key length in seconds for different settings of the alphabet Σ, the pattern p and the text T using fast-decryption Paillier [40].
Table 13. Performance results for 1024 and 2048 bit key length in seconds for different settings of the alphabet Σ, the pattern p and the text T using fast-decryption Paillier [40].







![Table 2. Detailed comparison with [14] and [16] for single-character wildcards and substring matching in malicious model with text length=n, pattern length=m, security parameter=k, rounds=Rds.](/figures/table-2-detailed-comparison-with-14-and-16-for-single-xf61t5xw.png)
![Table 3. Detailed comparison with [15] for non-binary substring matching in HBC model with text length=n, pattern length=m, security parameter=k, rounds=Rds.](/figures/table-3-detailed-comparison-with-15-for-non-binary-substring-2o93ac7o.png)


![Table 13. Performance results for 1024 and 2048 bit key length in seconds for different settings of the alphabet Σ, the pattern p and the text T using fast-decryption Paillier [40].](/figures/table-13-performance-results-for-1024-and-2048-bit-key-juynvcjx.png)