HAL Id: hal-01759108
https://hal.archives-ouvertes.fr/hal-01759108
Submitted on 5 Jun 2018
HAL is a multi-disciplinary open access
archive for the deposit and dissemination of sci-
entic research documents, whether they are pub-
lished or not. The documents may come from
teaching and research institutions in France or
abroad, or from public or private research centers.
L’archive ouverte pluridisciplinaire HAL, est
destinée au dépôt et à la diusion de documents
scientiques de niveau recherche, publiés ou non,
émanant des établissements d’enseignement et de
recherche français ou étrangers, des laboratoires
publics ou privés.
Handover Triggering in IEEE 802.11 Networks
Nicolas Montavont, Alberto Blanc, Renzo Efrain Navas, Tanguy Kerdoncu,
German Castignani
To cite this version:
Nicolas Montavont, Alberto Blanc, Renzo Efrain Navas, Tanguy Kerdoncu, German Castignani.
Handover Triggering in IEEE 802.11 Networks. IEEE 16th International Symposium on A World
of Wireless, Mobile and Multimedia Networks (WoWMoM), Jun 2015, Boston, United States.
�10.1109/WoWMoM.2015.7158126�. �hal-01759108�

Handover Triggering in IEEE 802.11 Networks
Nicolas Montavont, Alberto Blanc, Renzo Navas and Tanguy Kerdoncuff
Institut Mines Telecom / Telecom Bretagne
2, rue de la chataigneraie
35576 Cesson
Email: firsname.lastname@telecom-bretagne.eu
German Castignani
University of Luxembourg / SnT
4, rue Alphonse Weicker
L-2721 Luxembourg
Email: german.castignani@uni.lu
Abstract—The current and future IEEE 802.11 de-
ployment could potentially offer wireless Internet con-
nectivity to mobile users. The limited AP radio coverage
forces mobile devices to perform frequent handovers while
current operating systems lack efficient mechanisms to
manage AP transition. Thus we propose an anticipation-
based handover solution that uses a Kalman filter to
predict the short term evolution of the received power.
This mechanism allows a mobile device to proactively start
scanning and executing a handover as soon as better APs
are available. We implement our mechanism in Android
and we show that our solution provides a better wireless
connection.
I. INTRODUCTION
Due to the proliferation of Wifi hot-spots and com-
munity networks, we have recently observed a great
evolution of IEEE 802.11 networks especially in urban
scenarios. These 802.11-based networks allow mobile
users to get connected to the Internet, providing a high
throughput but a limited mobility due to the short cover-
age area of access points (APs). In our previous work [1]
we have shown that community networks appear to be
highly dense in urban areas, generally providing several
APs (15 in median) per scanning spot. Under this condi-
tion, a mobile user may be able to connect to community
networks and compensate the low AP coverage area
by transiting between APs. We call such AP transition
a handover. However, two main issues currently limit
mobile users from using community networks in such
a mobility-aware scenario. First, operators have not
deployed the necessary infrastructure to allow mobile
users to perform handovers without being disconnected
at the application layer, i.e., after a handover on-going
application flows are interrupted. This limitation may be
addressed by deploying a Mobile IP [2] infrastructure, in
which the application flows may be tunnelled through
a Home Agent that belongs to the operator. Second,
independently from the first issue, there is still a lack of
mechanism to intelligently manage a layer 2 handover
between two APs. In current mobile devices, when a
handover occurs, we observe a degradation of on-going
flows corresponding to a dramatic reduction of the TCP
congestion window (CWND) and of the throughput. In
this paper, we focus on this latter issue by analyzing
the impact of layer 2 handovers on mobile users. We
propose Kalman-filter-based HAndover Trigger algo-
rithm (KHAT) that succeeds in intelligently triggering
handovers and reducing the scanning impact on the
mobile device. We propose a complete implementation
of our handover mechanism in Android ICS (4.0) and
show a comparative study to show that our approach
outperforms the handover mechanism that is currently
implemented on these devices.
The paper is organized as follows. Section II
presents the litterature on handover optimization and
Section III analyzes the handover impact on on-going
communications. Section IV introduces KHAT which is
evaluated indoor and outdoor in Section V. Section VI
concludes the paper.
II. HANDOVER PROCESS AND RELATED WORK
The IEEE 802.11 standard defines a handover as a
three steps process: scanning, authentication and asso-
ciation. The standard proposes two different scanning
algorithms namely passive and active scanning. In pas-
sive scanning, the mobile station (MS) simply tunes its
radio on each channel and listens for periodic beacons
sent by the APs. In active scanning, the MS proactively
sends requests in each channel and waits for responses
during a pre-defined timer.
Once candidate APs have been found, the MS se-
lects one of the APs and attempts authentication and
association. If the association is successful, the MS
can send and receive data through the new AP, if this
new AP is on the same IP subnet as the previous AP.
If the new AP belongs to another IP subnet, the MS
needs additional processing to update its IP address
and redirect data flows to its new point of attachment.
Such Layer 3 handover may be handled by specific
protocols like Mobile IP [2]. Note that in this paper
we do not address IP mobility and any layer 3 mobility
management protocol can be use on top of our proposal
if needed.978-1-4799-8461-9/15/$31.00
c
2015 IEEE

In 2012, the IEEE has published new amendments
for IEEE 802.11 handover optimization, aimed at re-
ducing its duration and its impact on higher layers. The
IEEE 802.11k amendment proposes mechanisms for
radio resource measurement for seamless AP transition,
including measurement reports of signal strength (RSSI)
and load of nearby APs. Additionally, the IEEE 802.11r
amendment contains a Fast Basic Service Set Transition
(FT), which avoids exchanging 802.1X authentication
signaling under special conditions by caching authenti-
cation data.
While these features may enhance the handover per-
formance, they heavily rely on a cooperation between
APs, which might not always be a viable solution. In
addition, users may access various networks operated
by different providers. In that case, operators should
share network information and performance among
them, which is quite an unlikely scenario. In this paper,
we focus on MS-based solutions, where the MS itself
handles the handover without the help from the network.
Several works have been proposed in the literature so
far. In general, those studies cover different aspects of
the handover mechanism. We may group them into three
main categories:
• Handover triggering: when to decide that a
disconnection with the current AP will occur.
• AP discovery: how to search for APs on differ-
ent channels by minimizing the impact on the
higher layers.
• Best AP selection: with which AP to associate,
among the discovered ones.
The simplest mechanism to trigger a handover is to
monitor the RSSI as an estimation of the link quality
and start the handover process if the current RSSI is
lower than a pre-established threshold (commonly set
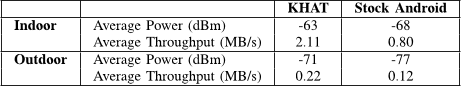
at −80 dBm). Fig. 1a shows the relationship between
the RSSI measured on an MS and the TCP throughput
that we have gathered during more than 600 connections
to community networks in a urban area in Rennes,
France [1]. We observe that the TCP throughput is ex-
tremely variable for high RSSI, but starts degrading for
RSSI lower than −70 dBm, and it becomes significantly
low around −80, dBm.
Some works focus on the anticipation of the han-
dover triggering in order to minimize the impact on
ongoing communications. Mhatre et al. [3] propose
a set of handover algorithms based on continuously
monitoring the wireless link, i.e., listening to beacons
from the current and neighboring channels. These ap-
proaches give handover latencies varying between 150
and 800 ms. However, since these approaches need to
listen to beacons from neighboring channels, it is neces-
sary to modify the firmware of the wireless card, which
may not always be possible. Yoo et al. [4] propose a
number of handover triggering mechanisms based on
predicting RSSI samples at a given future time using
Least Mean Square (LMS) linear estimation. In this
algorithm, the device continuously monitors the RSSI
and computes the LMS prediction if the RSSI is below
a certain threshold (P
Pred
). Then, if the predicted RSSI
value is lower than a second threshold, P
Min
, the MS
starts a handover.
Wu et al. [5] propose a handover mechanism aiming
at decoupling the AP discovery phase from the AP
selection and reconnection phase. The MS alternates
between scanning phases and a (normal) data mode
where the MS is connected to its current AP. The
time interval between two scanning phases is adapted
depending on the current signal level and varies between
100 and 300 ms. In each scanning phase, the sequence of
channels to scan is selected based on a priority list that
is built based on the results of a periodic full scanning
(i.e., here all channels are scanned).
As far as Android devices are concerned, Silva et
al. [6] present a mobility management solution based on
IEEE 802.21. They propose a mapping of IEEE 802.21
primitives for handover initiation, preparation, execution
and completion to existent Android OS methods and
functions.
III. HANDOVER IMPACT
During an L2 handover, the MS is not able to send
or receive application flows. This is because, usually,
when a MS triggers a handover, the link quality does
not allow exchanging frames anymore, and because
the MS is often switching operating channel. In this
section we evaluate the handover and scanning impact
on application flows, and determine which parameters
influence the scanning latency and success rate.
This testbed consists of nine Cisco Aironet 1040
APs installed in the roof of our building at the locations
given in Fig. 2. All APs are connected to a dedicated
wired LAN. APs broadcast a single SSID, correspond-
ing to an open-system authentication network belonging
to a single IP subnet. We also use a dedicated (fixed)
server for traffic generation and tracing. iPerf is used
to generate TCP downlink traffic to the MS. For each
experiment, we walk from AP
1
to AP
6
and then back
again to AP
1
.
A. Operating Systems Benchmark
To illustrate how the handover is currently impacting
data flows, we have performed a set of experiments
to evaluate the degradation of TCP performance for
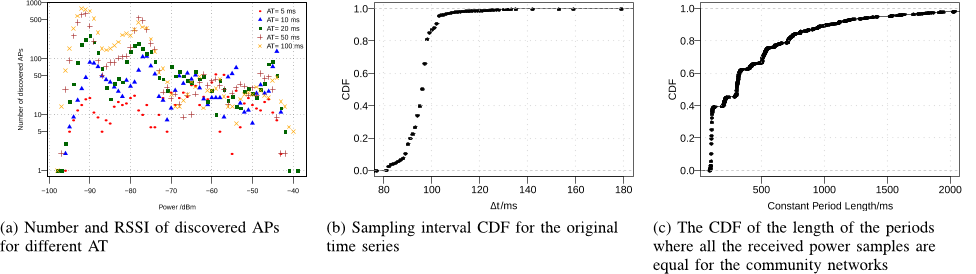
different devices and Operating Systems (OS). Table I
shows the number of handovers and the average TCP
2

-20
0
20
40
60
80
100
120
-90 -80 -70 -60 -50 -40 -30
Throughput / KB/s
Signal Strength / dBm
Throughput Std. Dev. Throughput Average
(a) RSSI and TCP Throughput Relation (b) Downloaded data for different OS
0 1 2 3 4
0
2
4
6
Time /s
Downloaded Data /MBytes
(c) Scanning impact on TCP download
Fig. 1: Various TCP performance
Fig. 2: Campus AP Deployment
throughput we have observed for the same path and
same MS speed using different devices and operating
systems. As a baseline, we also show the maximum
achieved throughput for each device remaining static
and connected to a single AP. Using Windows, we
observe the best result, since the MS performs up
to four handovers, reaching an average throughput of
0.875 MB/s. Additionally we observe that for Win-
dows, the time in which no data is downloaded (i.e., the
disconnected time) is relatively short compared to the
other OSs. The netbook running Ubuntu reacts slowly
to changing channel conditions: in this case the MS is
disconnected for more than 20 s and executes only two
handovers, indicating that the MS waits until the quality
of the radio link is significantly degraded. Fig.1b shows
the evolution of the downloaded data for each case.
Additionally, we have observed that for the Windows
device, the average round-trip time (RTT) is the lowest
one (103 ms) having also a low standard deviation. This
differs from the other devices that reach larger RTT
values.
B. Scanning Interactions with Data Traffic
We focus on active scanning where an MS sends
Probe Requests on each channel to discover potential
APs, instead of just waiting for periodic beacons (pas-
sive scanning). We chose active scanning because it
allows spending less time in each channel to determine
the AP availability. If the handover phases are done
one after the other, all packets that arrive during the
handover process will be lost. In order to reduce the
impact of handovers on applications flows, it is possible
to introduce a gap between the scanning phase and
the other handover steps, i.e., the decision to handover,
the authentication and the association, as presented
in [5]. An MS may use the power saving mode defined
in IEEE 802.11 to request its current AP to buffer
incoming packets during the time the MS scans other
channels. This way, instead of loosing packets during
the scanning phase, an MS can receive the packets after
the scanning phase, albeit with an extra delay. This
behavior is illustrated in Fig. 1c, where we plot the
sequence number of the received packets of a TCP flow
when an MS is performing one scan of the 13 channels
with an active timer set at 50 ms. We can see that the
scan is starting just before the time 1 s, at which no more
data packets are received from the server. Once the scan
is finished, around 850 ms after, the MS comes back to
its current AP, and starts receiving TCP packets again.
This technique can also be used to split a scanning
phase into several sub-phases where only a subset of
channels are scanned. For example, to scan the 13
channels, an MS could sequentially scan three times
a subset of 4 (or 5) channels each time, interleaving
these sub-phases with the data mode with the current AP
to retrieve data packets. The impact of the number of
scanned channels, and the timers used in each channel
is given in the next subsection.
C. Scanning Parameters
We analyze the scanning performance under differ-
ent values of timers used to wait for Probe Responses
(from 5 ms to 100 ms) and different number of scanned
channels during a sub-phase (between 1 and 13). In
the standard IEEE 802.11 scanning algorithm, the MS
is supposed to scan each channel using two timers
3

Device OS Version Chipset Static Avg. Mob. Avg. Number of Mean RTT σRTT
Thr. (MB/s) Thr. (MB/s) handovers (ms) (ms)
Asus N10J Win XP SP2 AR5006 5.19 0.878 4 103 43
Asus N10J Ubuntu 10.04 AR5006 4.88 0.601 2 161 360
Nexus S Android 4.0.3 BCM4329 3.80 0.568 5 129 114
MacBook MAC OS 10.7.4 BCM4322 8.44 0.613 3 167 276
TABLE I: Handover performance of different OS
Nb. of AT=5 AT=10 AT=20 AT=50 AT=100
channels (%) (%) (%) (%) (%)
1 3.11 5.76 10.62 22.28 25.24
3 6.45 18.28 32.61 58.18 88.24
5 9.28 21.02 38.83 68.94 89.31
8 10.44 23.61 40.46 70.43 96.58
13 11.74 28.62 45.76 79.88 100.00
RSSI -67.16 -70.07 -76.02 -81.28 -83.26
TABLE II: Percentage of discovered APs for different
values of AT and number of scanned channels
namely MinCT and MaxCT (see section II). However,
the IEEE 802.11 Android driver uses a single timer,
namely Active Timer (AT) for scanning. AT is defined as
the time an MS waits for Probe Responses on a channel.
We ran 60 scanning sub-phases for each AT and
subset of scanned channels and measured the average
number of discovered APs, the RSSI distribution of the
discovered APs and the average duration of the scanning
(i.e., the scanning latency). Results are presented in
Table II. As a baseline, we consider that all the available
APs are discovered when scanning the full channel
sequence (i.e., 13 channels) using AT=100 ms. In the
other cases, the MS discovers only a fraction of the
APs, since it either does not wait long enough to receive
all AP Probe Responses, or because only a subset of
channels are scanned.
We have also observed that when using a short
AT, even if the MS discovers a low number of APs,
those APs have a high RSSI. On the other hand, when
using higher AT values, the MS discovers more APs
but a large part of them have a low RSSI. This can be
observed in Fig. 3a, where we see that for AT=5 ms the
average RSSI of candidate APs is −67 dBm, while for
AT=20 ms, this decreases up to −76 dBm.
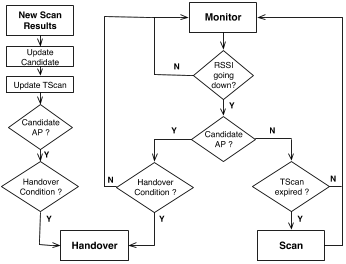
IV. KHAT: PROACTIVE HANDOVER ALGORITHM
We propose a handover algorithm called Kalman
Filter-based HAndover Triggering (KHAT for short) that
provides link going down detection, optmized scanning
strategy, and new AP selection. An MS monitors its
link quality with its current AP, and when the signal
strength is degrading, it starts alternating between scan
periods and data communication with the current AP.
The scan periodicity and the timer values are determined
according to the current link quality and whether a can-
didate AP has already been found. Once the candidate
AP becomes better than the current AP, the handover is
triggered.
A. RSSI modelling
One way of keeping track of the changing radio
condition is to track the RSSI on the MS. While far
from being perfect, the RSSI has the advantage of being
always available, whether the MS is exchanging data or
not, as it is updated not only whenever the MS receives
data frames but also when it receives beacon frames,
which are typically sent every 100 ms by most APs.
As the RSSI can fluctuate rapidly, especially when a
user is moving, its instantaneous value is not necessarily
representative. At the same time, its local average and
trend are more useful in deciding whether the radio
channel conditions are improving or not and whether
they are reaching the point where communication is no
longer possible. Using the well known Kalman filter,
it is possible to extract this information from the RSSI
measurements. Many authors have already use Kalman
filter and other time series techniques in order to model
radio channels and the received signal strength, see, for
example, the works by Jiang et al. [7], by Baddour et
al. [8] and references therein.
More formally, let X(t
i
) , X
i
be the received
signal strength at time t
i
. In our case, we sample
the RSSI roughly every 100 ms; but, as we rely on
software timers, there are no guarantees that the t
i
’s
will be equally spaced. Figure 3b shows the empirical
distribution of ∆t
i
= t
i
−t
i−1
for a subset of the traces
we collected. The average is 96 ms and the standard
deviation is 8.2 ms. Given that roughly 90% of the
samples are within less than 100 ms of each other, it
seems reasonable to “re-sample” the time series with a
time-step of 100 ms.
In all the traces we have collected, it is often the
case that several consecutive samples have the same
value, indicating that the received signal strength is
often constant during periods that are longer than the
average distance between samples. The presence of sev-
eral samples with exactly the same value is an obstacle
when one is trying to estimate the local trend of a signal
as, in this case, the estimated slope would be exactly
0. The Kalman filter does not perform well in these
circumstances. As we rely on the values reported by the
802.11 driver, we wondered whether these consecutive
samples with the same values were caused by the driver
4